

Communicate the inspiring things you’re doing, reach your members (and hear back).
People can give money by text message, on social media, on your church’s website, via QR code – all without having to log in or re-enter payment info.
Included FREE with all Flocknote plans!
Customize your member data, organize members into households, track attendance & participation, set parental contacts for children, and so much more!
Religious Education, Sacrament tracking, Sunday school, Family Registration, volunteer signups, ticket sales, event RSVPs, potlucks…and any other customized use you can come up with!
Capital campaigns, fundraising goals, advanced filtering, targeted smart communications, on-demand donor summaries, EOY tax reporting, and more.
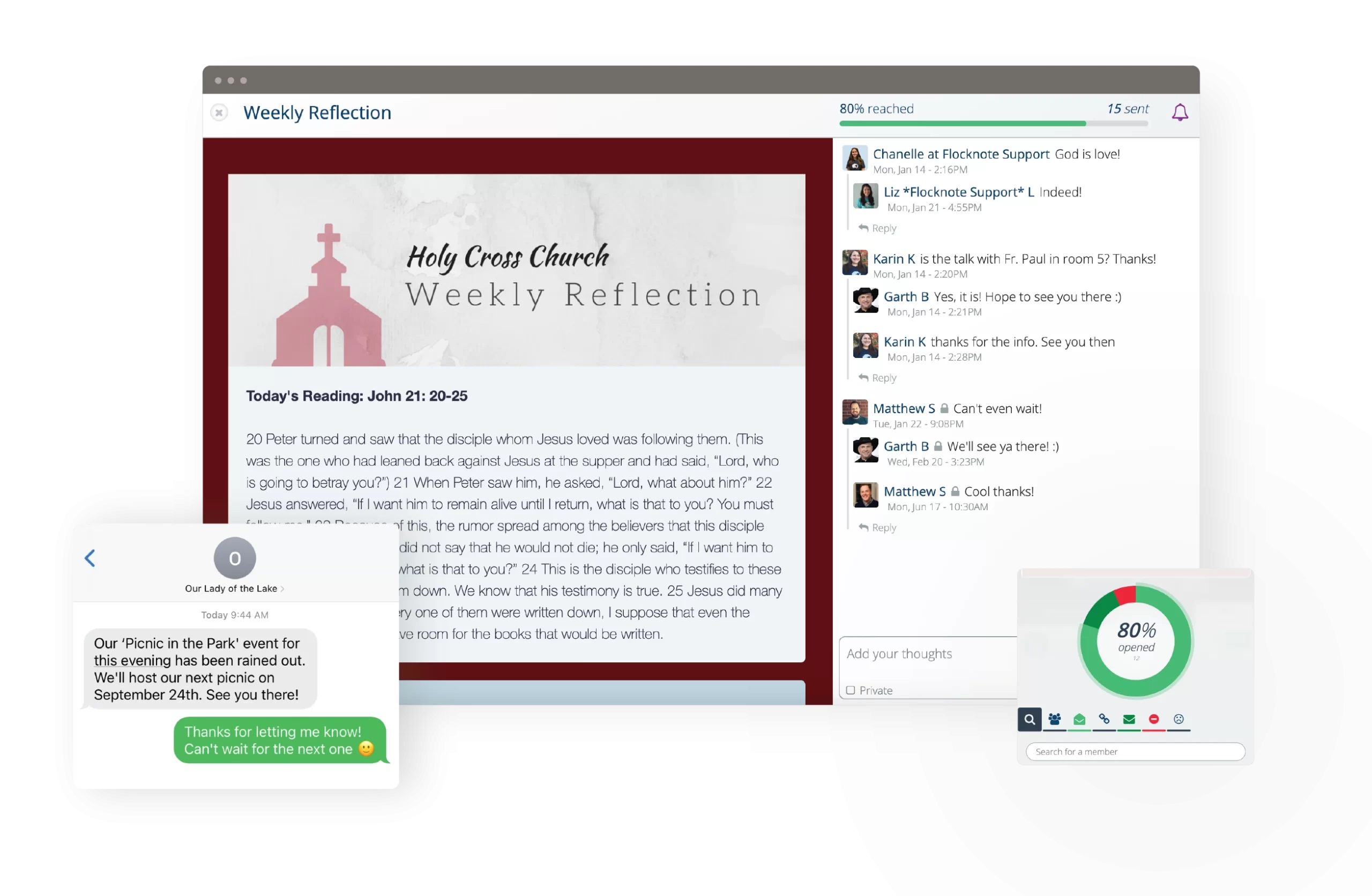






Seamless Communication
Reach your people, and hear back
Robust Member Management
Clean up your database (and keep it clean)
Secure Online Giving
Raise more money, faster than ever before
Advanced Signups
Modernize Registration and event signups
Free Content Library
Pre-made content from Flocknote & partners
Think of us as expert movers – we’ll carefully (and thoroughly) move your church data from its old home to its new home in Flocknote. We’ll even help unpack a bit!
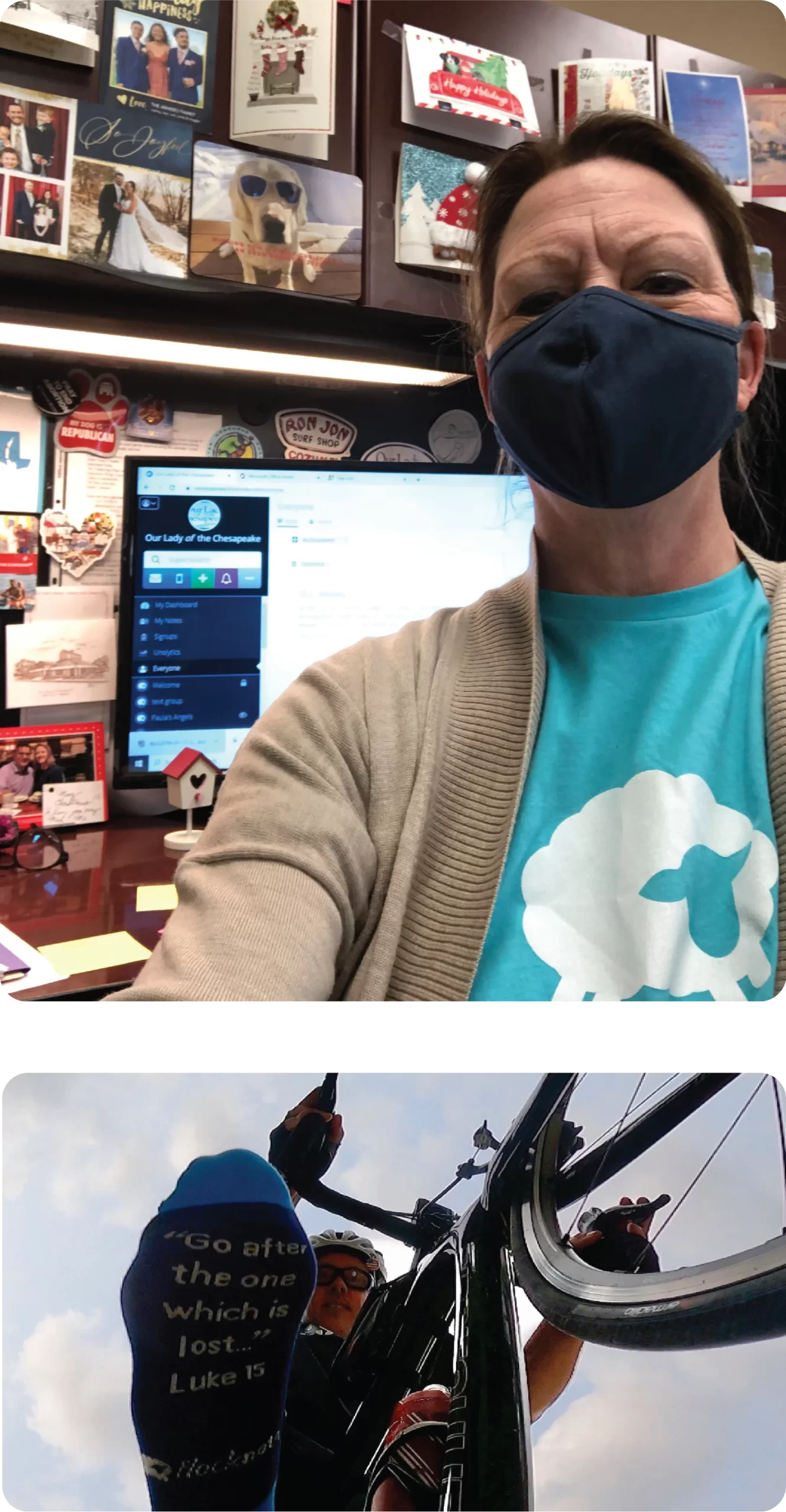
“This is the best way to handle emails and texts ever! These guys are knowledgeable, helpful and friendly. Thanks!”
Reine Overton | St. Elizabeth’s Church
Working with over 10,000 churches & 200,000 church and ministry leaders
Partnering with 50 + Diocesan and Archdiocesan partners in the U.S & Canada
100% employee-owned. Learn more about our mission and how we’re different.
Hi there!
I’m Matt, founder of Flocknote, and I’m glad you’re here. We hope you give our friendly software and award-winning customer service a try.
As a 100% employee-owned and mission-driven company that does no advertising or social media, we grow mostly by referrals from our 10,000 partner churches. Thank you for considering us as a partner and for all you do for the Church.
Gratefully,






Susanne O-Doherty | Spokane Cathedral Parish
Included in the Flocknote Starter package.